
Empowering Small Businesses with Apple Technology
At QCD, we specialise in helping small businesses unlock the full potential of Apple products. As certified Apple Consultants, we bring expert guidance and hands-on support to ensure your team is equipped, secure, and productive.
What We Do
🔧 Device Setup & Deployment
Whether you're onboarding a single MacBook or rolling out a fleet of new Macs, we handle the setup so your team can hit the ground running.
🔐 Mobile Device Management (MDM)
We implement robust MDM solutions to keep your Apple devices secure, compliant, and easy to manage—no matter where your team works.
💼 Business-Ready Configuration
From email and file sharing to app provisioning and network integration, we tailor every device to fit your business environment.
🧑💻 Ongoing Support & Consultancy
We’re not just here for the setup—we’re your long-term partner in navigating updates, scaling your tech, and solving Apple-related challenges.
Why Choose QCD?
✅ Apple-Certified Expertise
✅ Tailored Solutions for Small Businesses
✅ Fast, Friendly, and Professional Service
✅ Remote and On-Site Support Available

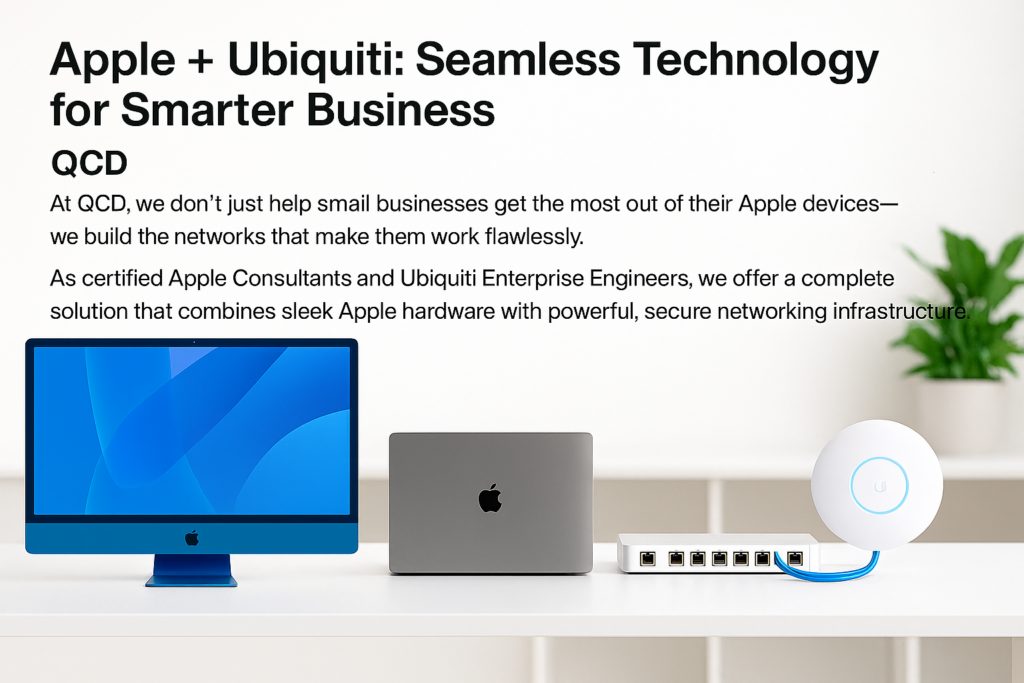
Integrated Apple & Ubiquiti Solutions
🖥️ Apple Device Setup & Management
From MacBooks to iMacs, we configure and deploy Apple devices tailored to your business needs, backed by robust Mobile Device Management (MDM).
🌐 Enterprise-Grade Ubiquiti Networks
We design and build secure, scalable networks using Ubiquiti Controllers, Switches, and WiFi access points—ensuring your Apple ecosystem runs smoothly and securely.
🔒 Security & Reliability
Our networks are built with business continuity in mind—secure, fast, and optimised for Apple environments.
🧠 Expert Consultancy & Support
Whether you're expanding your office or troubleshooting connectivity issues, our team is here to guide you every step of the way.
Central Bristol: 0117 20 33 925
North Somerset: 01275 541 893
prefer chat? WhatsApp: +447900894419
Address:
Foxhollow
175 Clevedon Road
Tickenham
BS21 6RG
